There is a moment in every large-scale eDiscovery matter when the sheer size of the dataset stops being a number and starts being a problem. Ten terabytes. Twenty terabytes. A petabyte. Sprawling across email servers, shared drives, collaboration tools, and forensic images, with duplicate files hiding in every corner and thousands of irrelevant system files polluting the corpus. This is the moment where eDiscovery deduplication and DeNIST processing stop being optional workflow steps and become the rate-limiting factor for your entire case.
Get them right quickly and defensibly, and you hand your review team a dataset that is lean, searchable, and ready for analysis. Get them wrong or get them done too slowly, and you are paying attorneys to review the same email 14 times in five different inboxes, while weeks slip off the calendar.
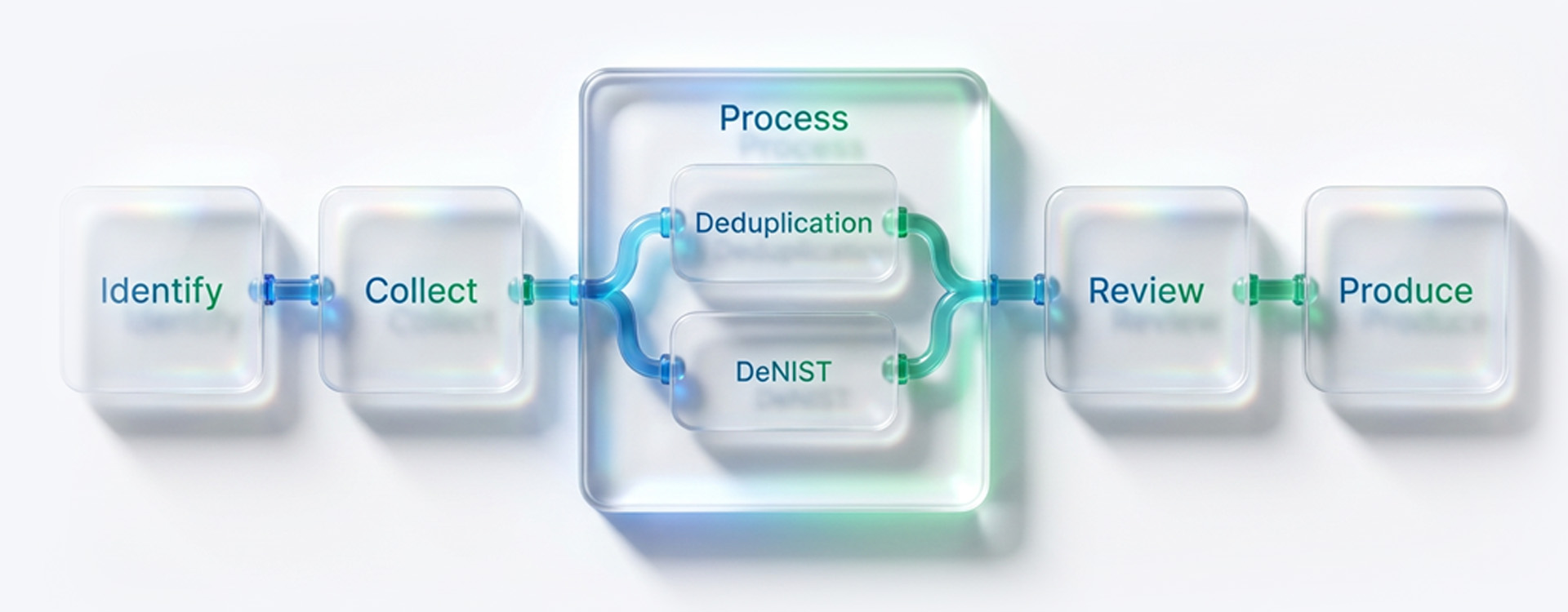
In this blog, we’ll cover everything legal teams and eDiscovery professionals need to know about deduplication and DeNIST processing: how they work, when to use each approach, what the technical mechanics actually mean, and why platform throughput at 10TB+ scale is the variable that separates fast, cost-controlled discovery from the alternative.
What Is eDiscovery Deduplication and Why Does It Matter at Scale?
When your legal team collects electronically stored information (ESI) from multiple custodians, duplicate files are not the exception. They are the rule.
Think about how email works at a typical company: a contract is drafted and shared with a team of six. Each recipient’s inbox now contains an identical copy. Add in a reply-all thread, a forwarded attachment, and a backup server snapshot, and that single document can appear dozens of times across a single collection.
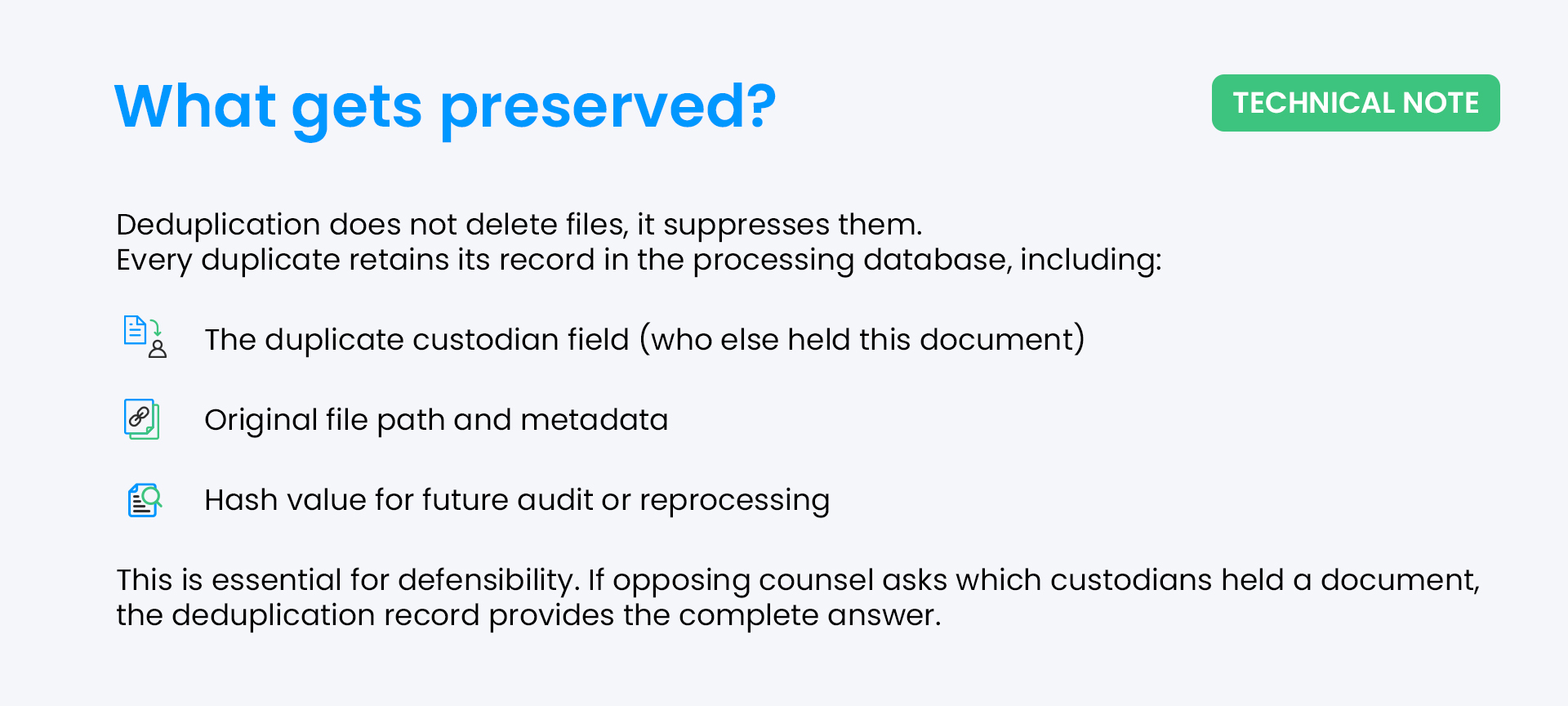
Deduplicating data is the process of identifying those identical files and suppressing redundant copies so that only one unique version is promoted to the review workspace. The rest are not deleted, they are archived, flagged, and tracked in a duplicate custodian field that preserves full chain-of-custody accountability.
At small data volumes, this is a convenience. At 10TB+, it is an economic necessity. Review costs represent 60-70% of total eDiscovery spending, and paying reviewers to examine the same document repeatedly is one of the most preventable expenses in litigation.
How Hash Value Deduplication Works
The technical mechanism behind deduplicating data is elegantly simple: each file is processed through a cryptographic hashing algorithm — most commonly MD5, SHA-1, or SHA-256 — which generates a unique fixed-length string based on the file’s binary content.
This string is the file’s digital fingerprint. Two identical files will always produce the same hash value. When the deduplication engine encounters a hash it has already seen, it suppresses the duplicate, records which custodians held copies, and sends only one instance to the review queue.
SHA-256 is increasingly the standard, offering stronger cryptographic integrity than MD5. Modern platforms like Venio generate hash values in parallel during ingestion, ensuring deduplication happens at speed without creating a processing bottleneck.
Global Deduplication vs. Custodian Deduplication: Which Should You Use?
This is the most consequential processing decision in most large eDiscovery matters, and it is one that legal teams often make without fully understanding the implications.
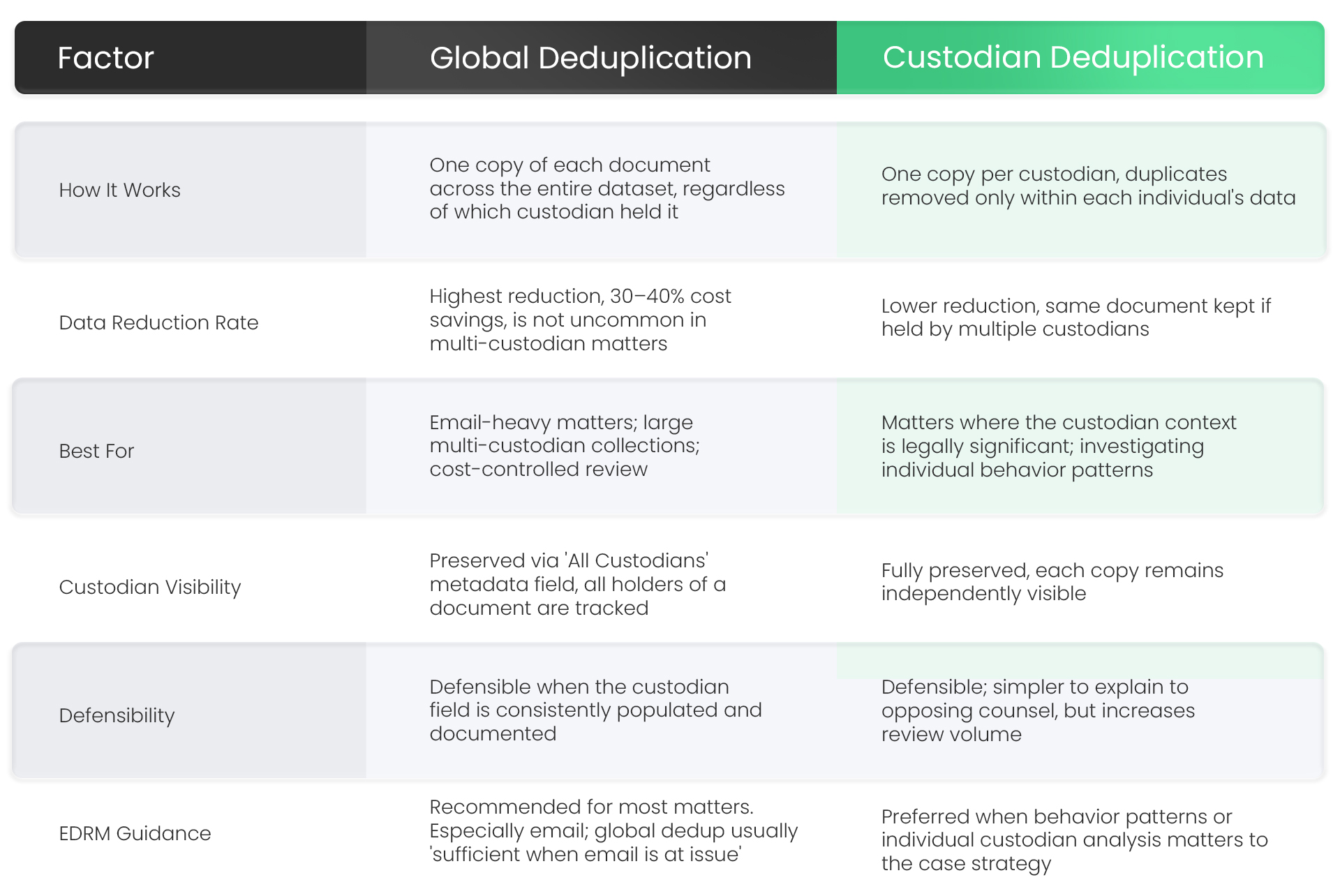
Global deduplication eDiscovery is the default for most high-volume matters because it delivers the greatest reduction in review volume without sacrificing accountability. The key is that all custodians’ fields must always be populated and preserved, this field is what makes global dedup defensible. If opposing counsel challenges your methodology, that field is your audit trail.
Custodian deduplication makes sense when the matter requires granular analysis of what specific individuals knew, held, or shared. For instance, in insider threat investigations or employment discrimination cases where the distribution of a document across custodians is itself evidence.
The decision should be made before processing begins and documented in your ESI protocol. Re-processing after the fact to change the deduplication scope is expensive and disruptive.
What Is DeNIST Processing and What Exactly Does It Remove?
Every computer, every server, every workstation, every forensic image contains thousands of files that have nothing to do with the matter at hand. Operating system components, software installers, browser cache files, and application libraries. On a typical corporate hard drive, these system files can account for a large proportion of the total file count, none of which has any evidentiary value.
DeNIST processing removes them automatically, at scale, before they ever enter your review workspace.
The name comes from NIST, the National Institute of Standards and Technology, and its National Software Reference Library (NSRL), a federal database of known, traceable application and system files identified by their cryptographic hash values.
When an eDiscovery platform runs DeNIST processing, it compares every file in the dataset against the NSRL hash list. Any match is flagged and excluded from processing.
The result: your review team never sees .exe files, .dll libraries, OS components, or any other system-generated content. They see only files that a human being created, modified, or interacted with, the only files that matter for discovery.
DeNIST vs. Deduplication — Different Tools, Same Goal
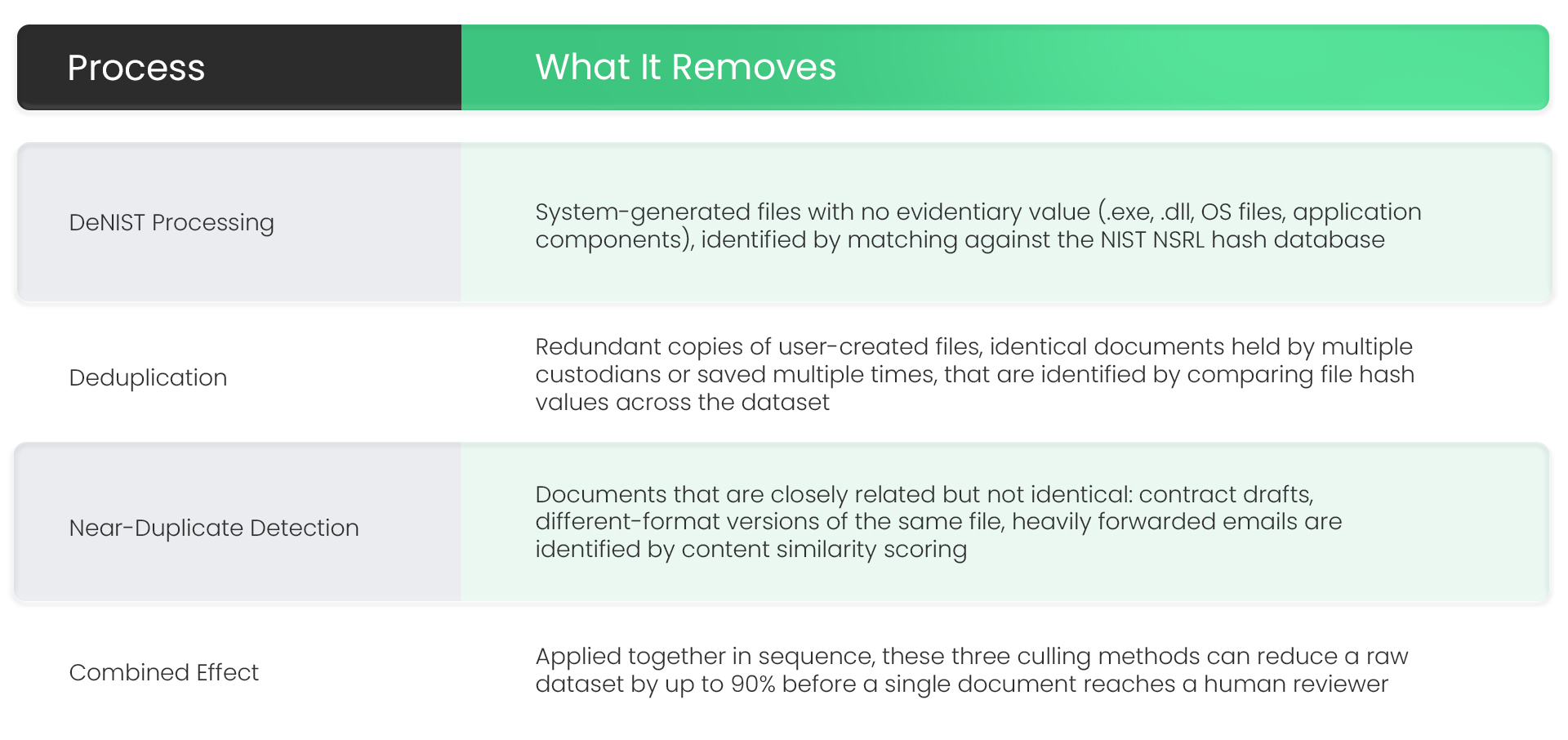
These are frequently confused because they operate at the same stage and achieve similar outcomes, but they target different problems.
Near-Duplicate Detection: The Third Layer of Intelligent Culling
Exact deduplication catches files with identical hash values. DeNIST removes system junk. But a significant portion of redundancy in any large dataset exists in a third category: near duplicates, files that are substantively the same but not technically identical.
A Word document and the PDF printed from it. A contract in its v1, v2, and v3 drafts. An email forwarded with a one-line addition. These files have different hash values because their binary contents differ, but reviewing each one separately creates enormous redundancy without proportionate analytical value.
Go Beyond Deduplication. Understand Your Data Faster.
Use clustering, threading, and analytics to reduce review volume before it begins.
Explore ECA CapabilitiesNear-duplicate detection uses content-similarity algorithms to group these documents, assigning a similarity score and identifying a ‘primary’ document within the group. Reviewers can then code the primary document and propagate that decision to near-duplicates, reviewing the group once instead of examining each version individually.
Venio’s platform incorporates near-duplicate detection and concept clustering into its analytics suite, enabling reviewers to identify and batch-tag document families that would otherwise escape exact deduplication filters.
Further combined with email threading, which groups related email conversations into reviewable threads rather than separate messages, these capabilities compound the efficiency gains from initial culling.
The Processing Speed Imperative, Why 10TB+ Datasets Change Everything
Processing speed is the variable that most eDiscovery professionals underestimate until they are in a large-scale matter with a hard deadline.
Consider the math: 10 terabytes of data can contain tens of millions of individual files, depending on the file type mix. A processing engine that handles 1TB per day means 10 days of processing before your review team sees a single document. Before early case assessment can begin. Before keywords can be tested. Before a culling strategy can be refined. Before any strategic decisions can be informed by actual data.
In litigation, that delay is not neutral. Deadlines do not pause for processing queues. Court-ordered production dates do not flex for infrastructure bottlenecks. And in regulatory investigations, every day a corpus sits unprocessed is a day of elevated risk.
This is why throughput, the number of terabytes a platform can process per day at full automation is not a marketing metric. It is an operational constraint that shapes what is possible in a matter.

At that throughput, a 10TB collection that would take 10+ days on a slower platform is processed in a single day. The review team gets access to a culled, deduplicated, DeNISTed dataset faster and that acceleration flows through every subsequent stage of the matter.
How Venio Handles Deduplication and DeNIST at Scale
The distinction between a platform that supports deduplication and one that automates it end-to-end at enterprise scale matters more than any feature checklist.
Venio’s processing engine automates the full culling workflow, DeNIST by file extension and unique digital signature, deduplication with metadata preservation during ingestion, and near-duplicate detection through built-in analytics, without requiring separate tool configurations, manual interventions, or post-processing cleanup steps.

This unified architecture matters for more than operational convenience. Every time data moves between tools, it creates a chain-of-custody gap, a potential security exposure, and an audit trail inconsistency. Keeping deduplication, DeNIST, and review in one platform eliminates those gaps entirely.
See How Teams Handle Massive Datasets Without Delays
Real-world results from high-volume matters with faster processing and lower review costs.
View the Case StudyBest Practices for Defensible Deduplication in eDiscovery
Deduplication decisions made at the processing stage echo through every subsequent phase of a matter. These best practices protect both efficiency and defensibility.
- Decide global vs. custodian scope before processing begins, re-processing after the fact is expensive and risks inconsistent results. Document the decision in your ESI protocol.
- Always populate and preserve the all custodians field for deduplicated documents. This field is your primary defensibility tool if the deduplication methodology is challenged.
- Apply DeNIST to parent-level (top-level) files only, never to child attachments. Breaking parent-child relationships to remove a system file creates a more serious integrity problem than the system file itself.
- Use near-duplicate detection as a second culling pass after exact deduplication, exact dedup reduces the corpus; near-dup detection groups the remainder for efficient batch review.
- Keep the NSRL database current, the NIST list is updated regularly, and running DeNIST against an outdated version means missing newly-cataloged system files.
- Generate and review a deduplication report before promoting the dataset for review, validate deduplication rates, check for unexpected outliers, and confirm the population of the custodian field before reviewers begin.
- Document everything, the deduplication methodology, hash algorithm used, scope (global or custodian), DeNIST version applied, and date of processing. This audit trail is your protection in a meet-and-confer or judicial challenge.
Can Your Platform Handle 10TB+ Without Slowing You Down?
Find out how leading vendors compare on processing speed, automation, and scalability.
See the 2026 eDiscovery Vendor Benchmark GuideAt Scale, Processing Speed Becomes Strategy
The fastest eDiscovery processing in the world is only valuable if the underlying culling is defensible. And the most defensible deduplication methodology is only valuable if it executes quickly enough to keep pace with the matter.
At the 10TB+ scale, these two requirements are non-negotiable simultaneously. That is why processing throughput, automated DeNIST, and defensible global deduplication eDiscovery are not separate capabilities to evaluate independently, they are a single integrated requirement that only a purpose-built, high-performance platform can fulfill.
Venio Systems delivers all three: the industry’s fastest confirmed processing throughput, automated deduplication and DeNIST at ingestion, and a unified data layer that keeps every step of the culling workflow inside one defensible, auditable system.
Whether you are processing a 10TB regulatory investigation or a 50TB second request, the same question applies: can your platform get from raw data to review-ready corpus without becoming the bottleneck? Want to learn more, contact us today!
Want experts to handle your data?
See exactly how Venio operationalizes AI across every stage of eDiscovery. No fluff, no generic pitch just a demo built around your workflow.
Book a Personalized Demo